-
Audit
In our firm we respond to the demands of our customers. We have modern methodologies and audit techniques operating in the best interests of your organization.
-
Statutory Audit
Audit services of the firm have been designed to support you to meet the challenges involved in managing risks, resources and information.
-
External Audit
The external audit service aims to express an independent opinion regarding the fairness of the financia!statements of the companies or certain business areas in which we use previously agreed procedures.
-
Managerial and Result External Audit
Our work consists of the execution of the defined procedures to review the accounting information and issue reports and documents.
-
Taxes
We work with our clients during all their processes to achieve an excellent statutory clase year, in order to optimize the taxes payment and ease the tax burden.
-
Transfer Pricing
The laws surrounding transfer pricing are becoming ever more complex, as tax affairs of multinational companies are facing scrutiny from media, regulators and the public.
-
Legal Services
Our legal advice involves professional lawyers, specialized in different fields.
-
Diagnosis and implementation of Full and SME IFRS
Servicio de Diagnóstico e implementación de NIIF plenas y NIIF para las PYMES.
-
Training and updating in IFRS
Services of Training and updating in IFRS
-
Calculation of accounting estimates under IFRS
Services of Calculation of accounting estimates under IFRS
-
Valuation of financial instruments
Services of Valuation of financial instruments
-
Advice on specialized topics
Services of Advice on specialized topics
-
IFRS advice for public sector entities
Services of IFRS advice for public sector entities
-
Preparation of financial statements and disclosures
Services of Preparation of financial statements and disclosures
-
Financial accounting
Only those who have clearly structured numbers and a good view of their business, can identify weaknesses and opportunities early enough to react on time to events in their environment.
-
Tax and legal compliance
The tax authorities constantly keep entrepreneurs and freelancers on alert, with tax issues taking part as a crucial role in almost all business decisions.
-
Due diligence
Due Diligence is a term, usually used in the field of business acquisitions, to refer to the process of finding information about an organization.
-
Valuations
The valuation of a company is not an exact science and can vary depending on the type of business and the reason.
Ethical Hacking, Penetration Testing and Vulnerability
Cybersecurity frames a set of tools, policies, security safeguards, guidelines, risk management methods, actions, training and in summary a series of practices that can be used to protect the organization's assets and users in cyber-environment. It is in this way that cybersecurity ensures that the security properties of the organization's assets and users are achieved and maintained against the corresponding security risks in cyber-environment.
Within the broad portfolio of services covered by the Information Security and Cybersecurity line that Grant Thornton in Colombia offers its clients, are the following:
Vulnerability scan
Identification of the vulnerabilities of the company's technological infrastructure through a complete analysis of the technological devices and processes. By performing open port detection, available services and known vulnerabilities in target information systems, together with manual and automatic false positive verifications, network weaknesses can be identified and reported on their failures, so that the organization has all the information necessary to take the accurate remediation measures.
Ethical Hacking
It consists of the controlled penetration (Penetration Test) of an organization's computer systems, in the same way as a hacker, but through a previously defined methodology, generating attacks on the technological infrastructure in a controlled manner and with due Authorization of the organization.
Infrastructure Assurance
Activities that are carried out to reinforce to the maximum possible the security of diverse devices critical for the IT infrastructure of the organizations. Servers, applications, active network equipment, operating systems, among others; Are subject to treatment to hinder the work of the attacker and gain time to be able to minimize the consequences of an imminent security incident and even, in some cases, prevent it from being fully realized.
Information Security Consulting
Grant Thornton in Colombia has a team of expert consultants dedicated to advisory and working together with clients in the evaluation, planning, assurance and control of the security of information assets aligned to international standards, best IT management practices and current regulations (ISO 27001, ISO 22031, MAGERIT, PCI DSS, among others).
Within the scope of the services we offer our clients are:
- Advice, design, evaluation and implementation of:
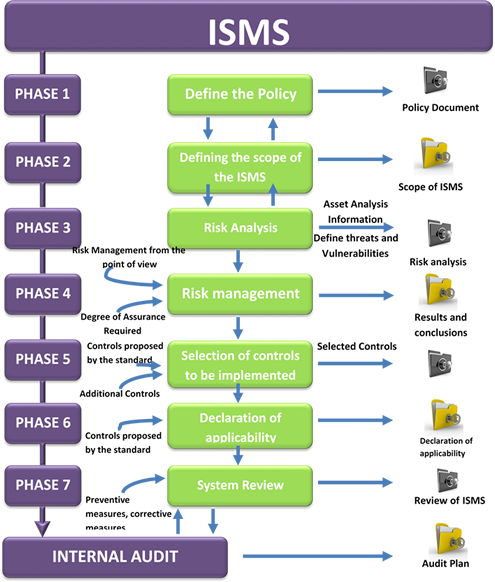
- Information Security Management Systems (ISMS)
- Business Continuity Plan (BCP)
- Risk Management
- Security Outsourcing
- GAP Analysis ISO 27001 - 27002, Analysis of maturity level
- Security incidents and response
OSSTM (Open Source Security Testing Methodology Manual)
The Open Method of Security Testing (OSSTMM) is one of the most complete and commonly used professional standards in Security Audits to review System Security from the Internet. It includes a framework that describes the phases that should be performed for the execution of the audit. It has been achieved thanks to a consensus among more than 150 international experts on the subject, who collaborate with each other through the Internet.

OWASP (Open Web Application Security Project)
Test methodology focused on application security, the framework described in this document aims to encourage people to evaluate and take a measure of security throughout the development process. Thus, they can relate the costs of unsafe software to the impact it has on their business, and thus manage appropriate business decisions (resources) for risk management.
PCI DSS (Payment Card Industry Security Standard)
This standard has been developed by a committee composed of the major credit and debit card companies, a committee called PCI SSC (Payment Card Industry Security Standards Council) as a guide that helps organizations that process, store and / or transmit Cardholder data (or cardholders), to secure such data, in order to avoid fraud involving debit and credit payment cards.
Methodology
All of our Cybersecurity and Information Security services offered by Grant Thornton in Colombia are performed with the evaluation and implementation of the best recognized standards and methodologies worldwide, among which are:
ISO 27001: 2013
ISO 27001 is an international standard issued by the International Organization for Standardization (ISO) and describes how to manage the security of information in a company, which comprises the following phases: